Explain asymmetric vs symmetric encryption in interviews: core differences, when to use each, real-world examples.
What is asymmetric vs symmetric encryption and why does it matter in interviews
Understanding asymmetric vs symmetric encryption shows interviewers you can connect theory to secure system design. Interviewers for software engineering, cybersecurity, or systems roles often probe crypto basics because these concepts reveal your grasp of confidentiality, integrity, and performance trade‑offs. For example, symmetric algorithms like AES are used for bulk encryption, while asymmetric schemes like RSA or ECC handle key exchange and digital signatures — the combination underpins TLS/HTTPS, a common system-design interview topic The SSL Store IBM.
Quick interviewing tip: name concrete algorithms (AES, RSA, ECC), give a one‑sentence use case for each, and sketch a hybrid flow (public key handshake then symmetric session). That short, concrete answer separates vague candidates from confident explainers.
What is symmetric encryption in the context of asymmetric vs symmetric encryption
Symmetric encryption uses a single secret key for both encryption and decryption. That design makes symmetric ciphers fast and efficient, ideal for encrypting large volumes of data (disk encryption, database fields, bulk file transfers). Common symmetric algorithms include AES, DES (legacy), and Blowfish AxCrypt IBM.
Key interview points about symmetric encryption:
- One shared key between parties must remain secret. The primary risk is secure key distribution.
- Computationally inexpensive: low CPU and memory costs, suitable for high-throughput use.
- Typical strong choice today: AES with 128‑ or 256‑bit keys for confidentiality.
Practice line: "Symmetric encryption like AES is best when you already have a secure way to share a key, because it's much faster for bulk data."
What is asymmetric encryption in the context of asymmetric vs symmetric encryption
Asymmetric encryption uses a public-private key pair: one key (public) can be shared openly for encryption or signature verification, and the other (private) remains secret for decryption or signing. Because it avoids secret key exchange, asymmetric crypto is ideal for establishing trust between strangers and for digital signatures (authenticating a sender) The SSL Store GeeksforGeeks.
Important interview facts about asymmetric encryption:
- Public keys are distributable; private keys must never be leaked.
- Algorithms (RSA, ECC) are computationally heavier and use longer key lengths to reach comparable security to symmetric keys.
- Asymmetric crypto is commonly used for key exchange, identity verification, and signing rather than bulk encryption.
Practice line: "Asymmetric schemes like RSA or ECC solve the key distribution problem and provide digital signatures, but are too slow for encrypting gigabytes directly."
How do asymmetric vs symmetric encryption compare side by side
Use this quick reference when an interviewer asks for a comparison — it's scannable and precise.
| Aspect | Symmetric Encryption | Asymmetric Encryption | |-------------------------|-----------------------------------------------|---------------------------------------------| | Keys Used | Single shared key (The SSL Store, AxCrypt) | Public-private pair (The SSL Store, GeeksforGeeks) | | Speed | Faster, simpler algorithms; ideal for large data (IBM) | Slower due to complex math, longer keys (Keyfactor) | | Security | Risky key exchange; secure with strong keys (e.g., 256-bit AES) (Keyfactor) | Safer for exchange (no private sharing); requires larger keys (e.g., 2048-bit RSA equivalence) (The SSL Store) | | Resource Use | Low; efficient for bulk (IBM) | High; practical for small payloads and key material (GeeksforGeeks) | | Examples | AES, DES, Blowfish (AxCrypt) | RSA, ECC, Diffie-Hellman (The SSL Store) | | Key Management | Secure sharing required (Keyfactor) | Public shareable; private stays secret (GeeksforGeeks) |
When you speak this aloud in an interview, say: "Symmetric is fast and efficient for bulk data but needs secure key exchange; asymmetric solves exchange and enables signatures but is slower and used for small payloads."
What are the strengths, weaknesses, and security nuances of asymmetric vs symmetric encryption
Interviewers expect nuance beyond "fast vs safe." Address key size equivalence, attack surfaces, and real-world caveats.
Key nuances to mention:
- Key size equivalence: a 256‑bit symmetric key gives security comparable to multi‑kilobit asymmetric keys (e.g., 3072‑bit RSA) — this helps explain why asymmetric needs larger key sizes for comparable strength Keyfactor.
- Attack surface: symmetric crypto is vulnerable at the key distribution step; asymmetric is vulnerable to private key compromise or poor randomness used in key generation.
- Performance trade-offs: asymmetric operations (encryption/signature) are computationally expensive, so systems use asymmetric crypto to bootstrap symmetric keys and then switch to symmetric for bulk operations (the hybrid approach).
- Algorithm lifecycle: older symmetric algorithms like DES are deprecated; choose AES or modern authenticated encryption (AES‑GCM) when you talk about confidentiality + integrity IBM.
Pro interview pro tip: mention authenticated encryption (AEAD) such as AES‑GCM or ChaCha20‑Poly1305 to show you understand authenticity+confidentiality, not just raw encryption.
How are asymmetric vs symmetric encryption used in real world systems and hybrid setups like HTTPS
Explain TLS/HTTPS as a canonical hybrid: asymmetric crypto authenticates the server and performs a secure key exchange; symmetric crypto encrypts the application data once a session key is established.
How HTTPS uses both:
1. Client fetches server certificate (public key) — asymmetric for authentication.
2. The client and server derive a shared symmetric session key (via RSA key transport, Diffie‑Hellman, or ECDHE).
3. Application data is encrypted with symmetric algorithms (AES or ChaCha20) for speed. This handshake pattern is central to secure web traffic and is often a follow-up interview question about "why hybrid?" The SSL Store Keyfactor.
Use cases to cite in interviews:
- Symmetric: disk/volume encryption, database field encryption, large file transfer (AES).
- Asymmetric: SSL/TLS handshakes, secure email (PGP uses both), digital signatures and certificate chains (RSA/ECC).
- Hybrid: VPNs and secure messaging apps (asymmetric for key exchange + symmetric for messages).
Practice explanation: "HTTPS demonstrates asymmetric vs symmetric encryption working together — the asymmetric phase sets up a temporary symmetric key, which is then used to efficiently encrypt the session."
What common interview traps should you avoid when discussing asymmetric vs symmetric encryption
Avoid these pitfalls that commonly cost candidates credibility.
Trap 1 — Oversimplifying security:
- Saying "asymmetric is always more secure" is wrong. Security depends on algorithm, key sizes, implementation, and context. Counter with key-size comparisons (e.g., 256‑bit symmetric ≈ 3072‑bit RSA) and mention quantum concerns only if asked.
Trap 2 — Confusing key exchange with encryption:
- Be clear: symmetric crypto needs a secure key-exchange mechanism; asymmetric cryptography solves distribution but is not a bulk data solution.
Trap 3 — Skipping authenticated encryption:
- Interviewers often expect you to mention integrity/authentication. Bring up AEAD modes (AES‑GCM) or MACs to show completeness.
Trap 4 — No examples or numbers:
- Use concrete algorithms and key sizes. "AES‑256" and "RSA‑2048/3072" are easy wins.
Trap 5 — Ignoring performance constraints:
- If asked how you'd secure a streaming system or a database, mention CPU costs, memory limits, and hybrid approaches.
How to avoid these traps:
- Prepare a 30–60 second script that cites algorithms, use cases, and a concrete hybrid flow.
- Sketch a small diagram on a whiteboard to illustrate key paths and trust anchors.
- If you don’t know a detail, say how you would find it: "I'd check algorithm recommendations from NIST or library docs, and prefer AEAD primitives."
How can you practice explaining asymmetric vs symmetric encryption with scripts and whiteboard demos
Actionable rehearsal plans to level up quickly.
Memorization hack (mnemonic): "Symmetric = Same key, Speedy for Secrets; Asymmetric = Public/Private, Perfect for Public channels." Repeat aloud and pair with a sketch.
Interview script example (60–90 seconds):
- "Symmetric encryption like AES uses a single shared key to encrypt/decrypt and is ideal for bulk data because it's fast. The downside is safe key distribution. Asymmetric encryption, like RSA or ECC, uses a public and a private key pair; public keys can be shared freely, which solves distribution and enables digital signatures, but it's slower and used for small payloads. In practice, systems use asymmetric crypto to exchange or derive a symmetric session key, then use symmetric encryption for the session — that's how TLS works."
Whiteboard demo steps:
1. Draw two parties (Client, Server).
2. For symmetric-only: show one shared key arrow; label "key exchange risk."
3. For asymmetric: draw public keys outgoing, private keys hidden; show encryption/decryption arrows.
4. For hybrid (HTTPS): show certificate → key exchange → symmetric session key → bulk data encryption.
5. Annotate performance and typical algorithms.
Practice questions to rehearse:
- "When would you pick symmetric over asymmetric?" — Answer: When you already have a secure key or need speed for large data.
- "How does HTTPS use both?" — Give the handshake → session key → symmetric data flow.
- "What is an authenticated encryption mode and why use it?" — Answer: AEAD like AES‑GCM provides encryption + integrity.
Self-test exercise:
- Explain the hybrid HTTPS flow to a non‑technical friend in 60 seconds. If they get the gist, you’re clear.
How Can Verve AI Copilot Help You With asymmetric vs symmetric encryption
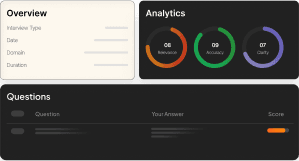
Verve AI Interview Copilot can simulate technical interviews where you explain asymmetric vs symmetric encryption, giving instant feedback on clarity and correctness. Verve AI Interview Copilot offers targeted practice prompts, common follow‑ups, and scoring so you can refine your explanation under time pressure. Use Verve AI Interview Copilot to rehearse whiteboard demos, practice the HTTPS hybrid flow, and get suggestions for stronger phrasing https://vervecopilot.com
What Are the Most Common Questions About asymmetric vs symmetric encryption
Q: What is the main difference between symmetric and asymmetric encryption A: Symmetric uses one shared key; asymmetric uses a public/private key pair.
Q: When should I use symmetric over asymmetric A: Use symmetric for large data when a secure key is available; it’s much faster.
Q: How does HTTPS use asymmetric vs symmetric encryption A: Asymmetric authenticates and exchanges keys; symmetric encrypts the session data.
Q: Is asymmetric always safer than symmetric A: Not necessarily; security depends on key size and implementation details.
Q: What algorithms should I name in an interview A: Say AES for symmetric, RSA/ECC for asymmetric, and mention AES‑GCM or ChaCha20‑Poly1305 for AEAD.
Q: How do I explain key size equivalence briefly A: Say: "A 256‑bit symmetric key approximates multi‑kilobit RSA strength (e.g., 3072‑bit)."
Conclusion
To ace crypto questions, prepare a concise, concrete explanation of asymmetric vs symmetric encryption that covers: what each does, practical trade‑offs (speed vs distribution), real‑world hybrids like HTTPS, and concrete examples (AES, RSA, ECC). Practice a 60–90 second script, draw a simple whiteboard handshake, and rehearse common followups about authenticated encryption and key sizes. Citing algorithm names and a hybrid flow shows both theoretical knowledge and system‑level thinking — exactly what interviewers and stakeholders want to hear.
Further reading and references:
- The SSL Store overview of asymmetric vs symmetric encryption: https://www.thesslstore.com/blog/asymmetric-vs-symmetric-encryption/
- GeeksforGeeks comparison and definitions: https://www.geeksforgeeks.org/computer-networks/difference-between-symmetric-and-asymmetric-key-encryption/
- IBM on symmetric encryption and real‑world usage: https://www.ibm.com/think/topics/symmetric-encryption/
- Keyfactor discussion on tradeoffs and key sizes: https://www.keyfactor.com/blog/symmetric-vs-asymmetric-encryption/
Kevin Durand
Career Strategist